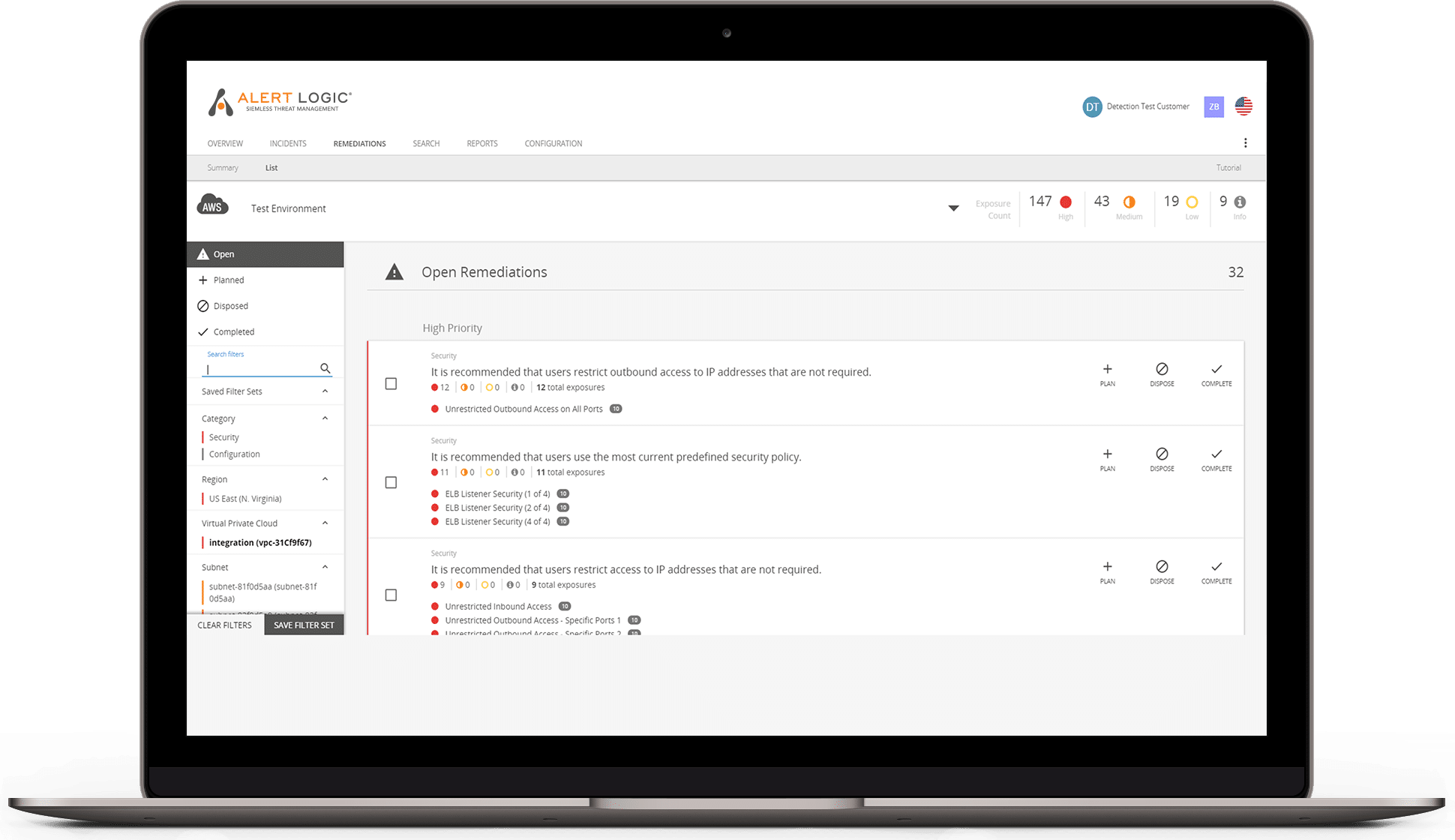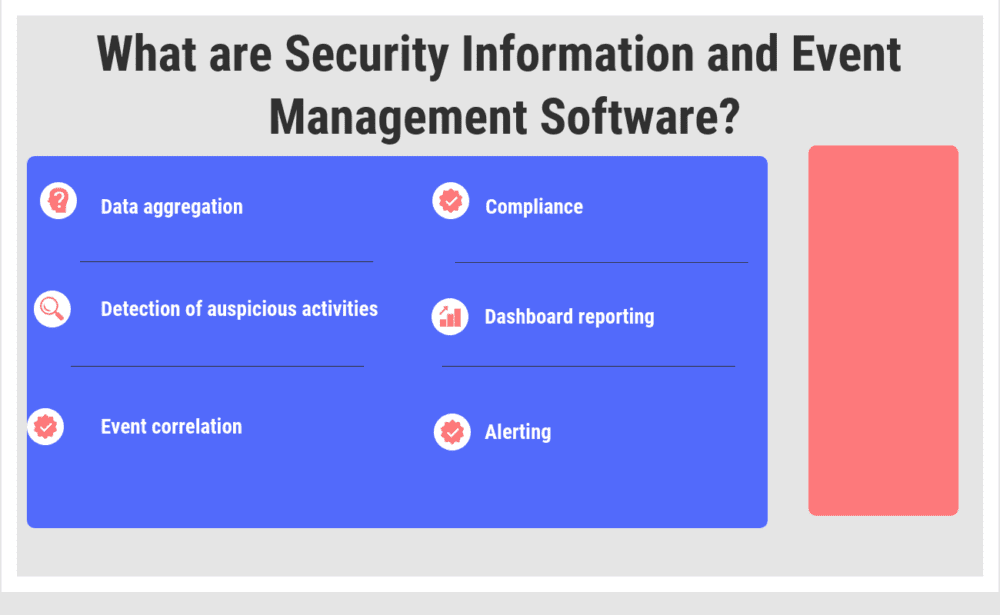
Top 22 Security Information and Event Management Software in 2021 - Reviews, Features, Pricing, Comparison - PAT RESEARCH: B2B Reviews, Buying Guides & Best Practices
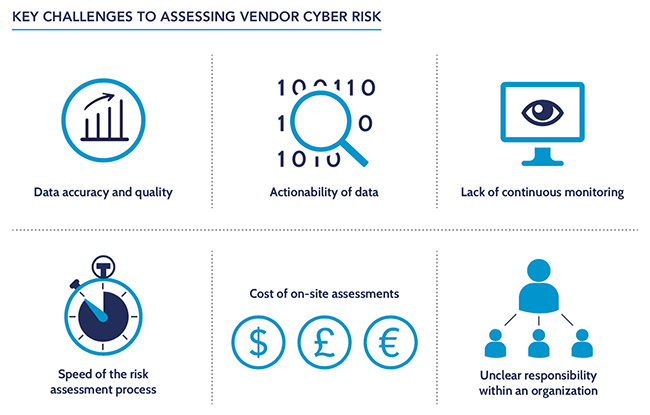
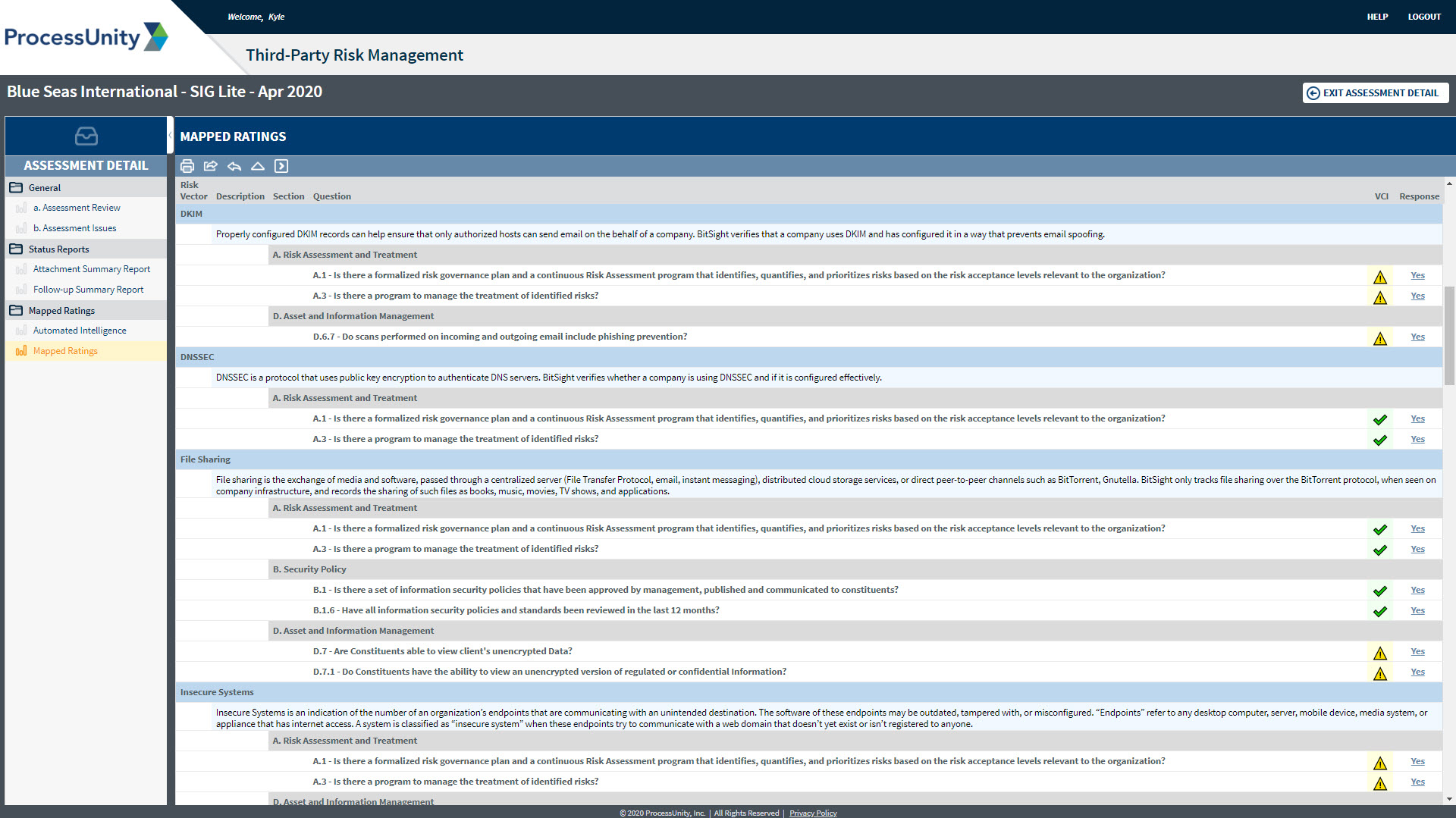
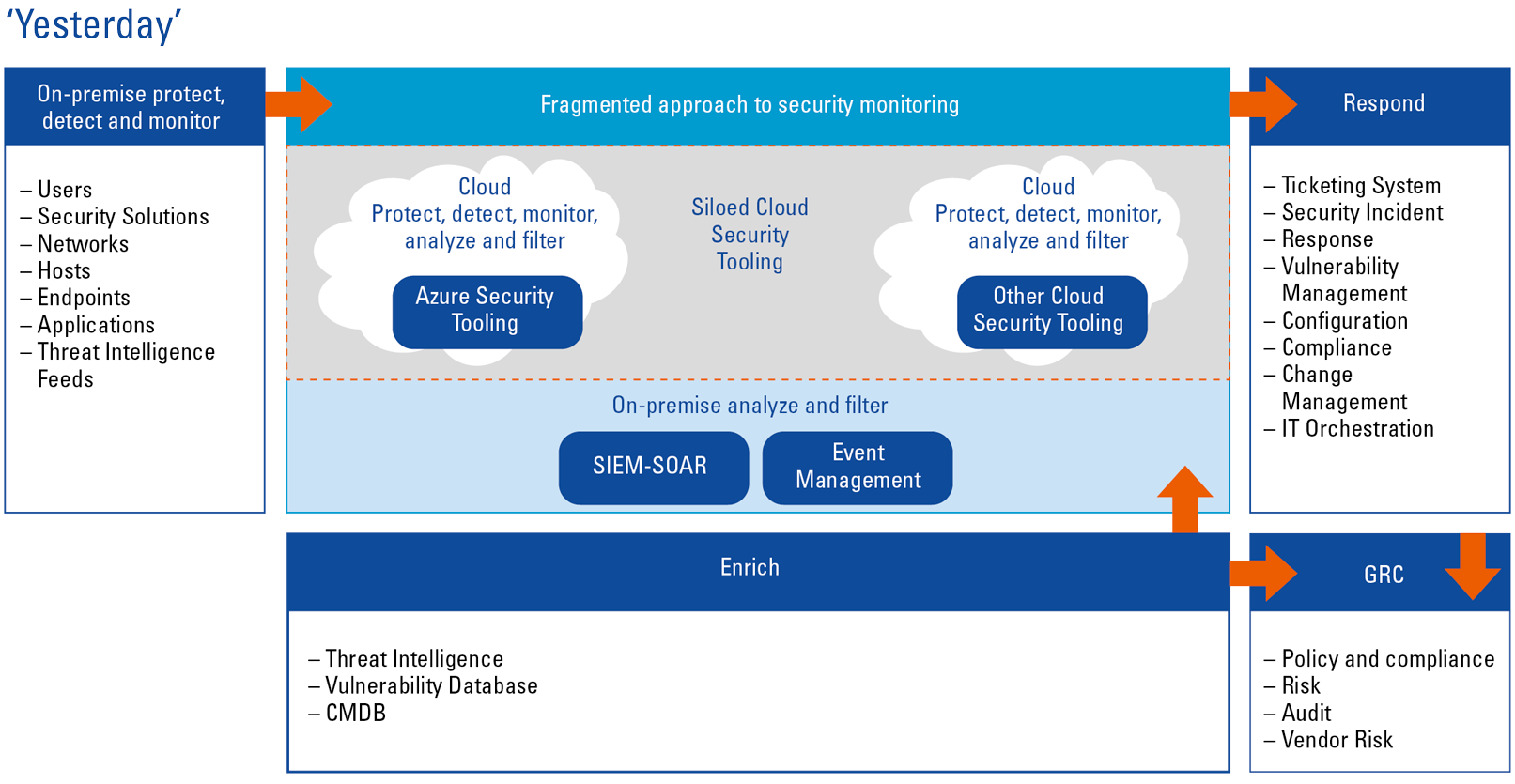
Current and emerging third-party cyber risk management approaches and challenges - Help Net Security